CVE-2022-21500 and Your Oracle E-Business Suite
Something exciting happened a few days ago. It started with a tweet and a blog post, and has evolved into an official CVE-2022-21500. I thought it would be good to publish some details beyond the official MOS note document.
Background
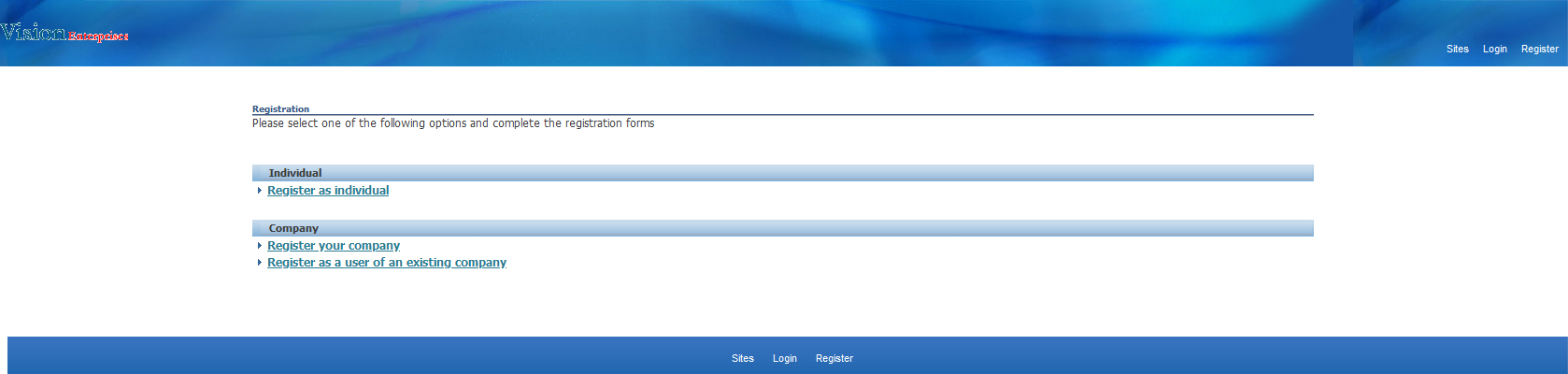
The mentioned blog post contains a description of how to:
- Easily create a new user in the Oracle E-Business Suite system (which might not be OK for the externally exposed systems).
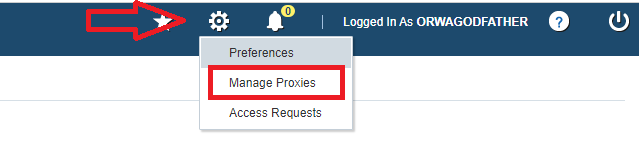
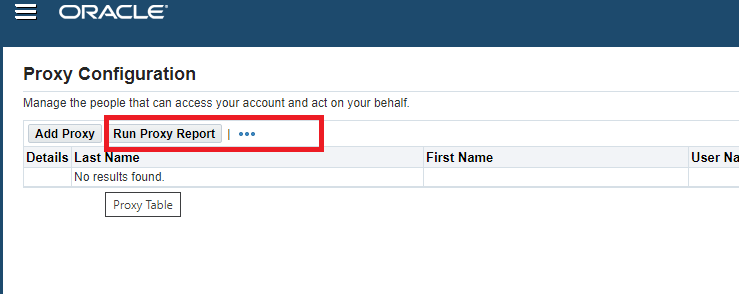
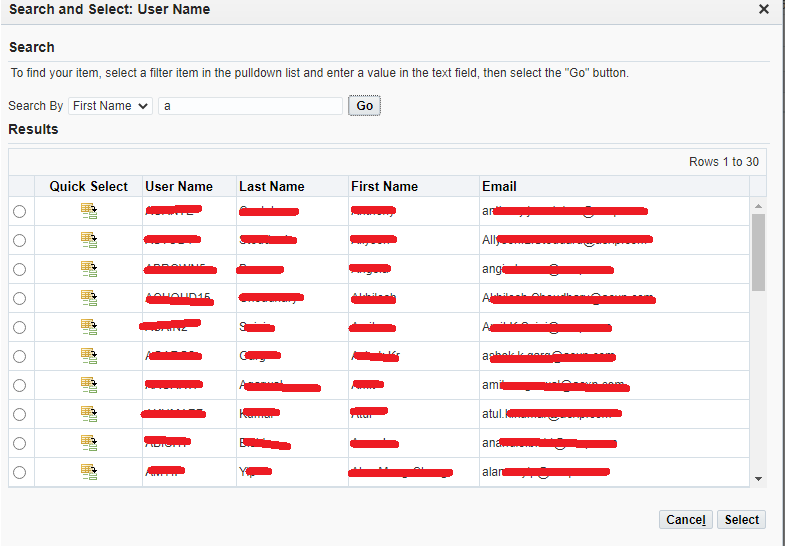
- Use the impersonation framework (proxy) to access the entire user directory of the system.
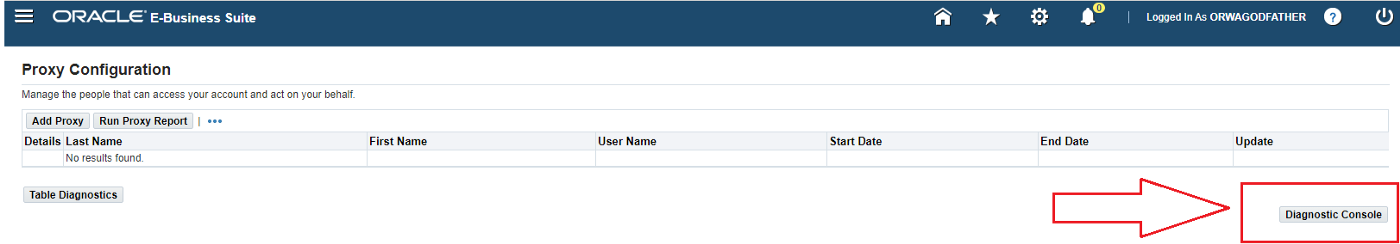
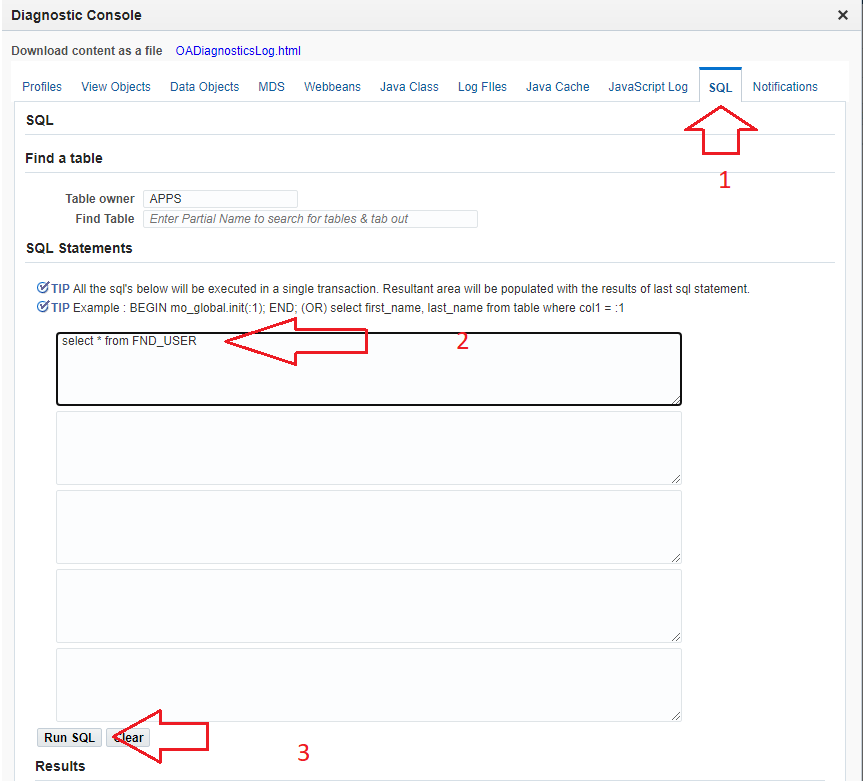
- Use FND Diagnostics and at the same time, run a SQL query (FND_USER full data query in the author’s example).
I am copying some of the screenshots from the author’s blog post:
We’ve come up with a handy cross-check-list.
1. Is there an external exposure?
Evaluate if your system is exposed to the public internet. If it is, the severity of this case may have the highest priority.
Some of our clients do have the additional Identity Gateways on top of the EBS system built for external access (like Onelogin or ForgeRock), which doesn’t let anyone reach EBS unless authenticated. So it was identified as a great preventive measure for such unauthorized exposure.
2. Remove the local login page self-registration link
https://ebs.domain.com/OA_HTML/AppsLocalLogin.jsp
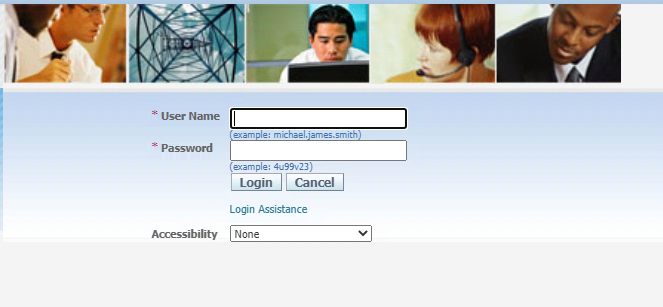
R12.1 does not have the new user registration link. The login assistance link may be removed via the personalization update.
R12.2 has an easier way of removing unnecessary links. Please reference How To Personalize Login Page To Show Or Hide Links on EBS 12.2.5+ (Doc ID 2105595.1).
The Local Login Hide Items profile option can be set to exclude both.
SELECT o.profile_option_name, u.user_profile_option_name, v.level_id, v.level_value, v.last_update_date, v.profile_option_value
FROM apps.fnd_profile_options o, apps.fnd_profile_options_tl u, apps.fnd_profile_option_values v
WHERE o.profile_option_name = u.profile_option_name
AND o.profile_option_id = v.profile_option_id
AND u.language = 'US'
AND o.profile_option_name like 'FND_LOGIN_HIDE'
AND v.level_id = 10001
ORDER BY 1;
declare
x boolean;
begin
x:=FND_PROFILE.SAVE('FND_LOGIN_HIDE', '#ForgotPasswordURL, #RegisterHereURL', 'SITE');
commit;
end;
/
3. Disable ibeCAcpSSOReg.jsp if iStore is not in use
https://ebs.domain.com/OA_HTML/ibeCAcpSSOReg.jsp
A bad sign and exposed user self-registration.
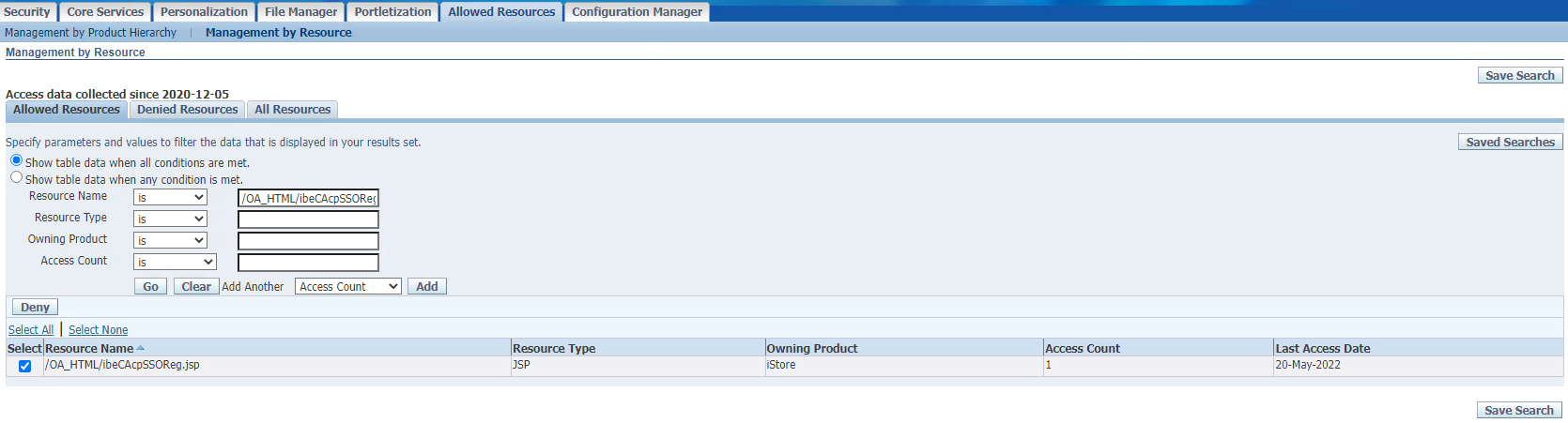
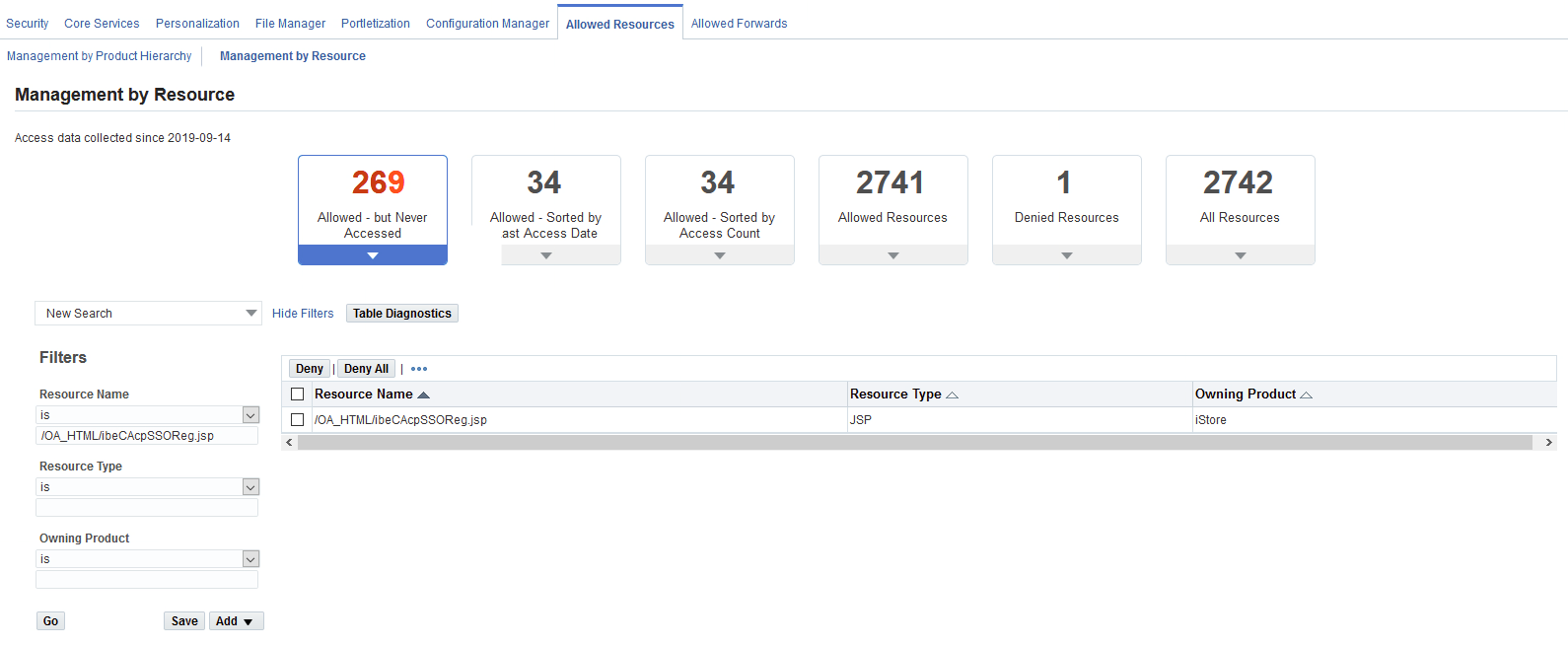
A good sign: you’re protected by the Allowed Resources framework.
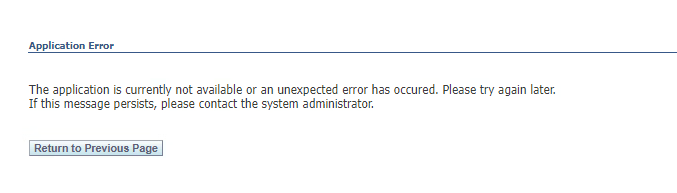
A not-so-good sign: you’re not protected by the Allowed Resources framework, it’s missing, but your configuration is causing an error:
Access the Allowed Resources configuration under the Functional Administrator responsibility, search for resource name /OA_HTML/ibeCAcpSSOReg.jsp and deny it:
Or you can apply a workaround by adding the below section to your httpd.conf file and forbidding the page.
# Custom deny of /OA_HTML/ibeCAcpSSOReg.jsp
<IfModule mod_rewrite.c>
RewriteEngine on
RewriteCond %{REQUEST_URI} ^/OA_HTML/ibeCAcpSSOReg.jsp.*
RewriteRule .* - [F]
</IfModule>
4. Limit the impersonation/manage proxies options
E-Business Suite R12 : Steps To Remove Functions ‘Access Requests’ And ‘Manage Proxies’ From The ‘Preferences’ Page (Doc ID 2182942.1)
R12.1
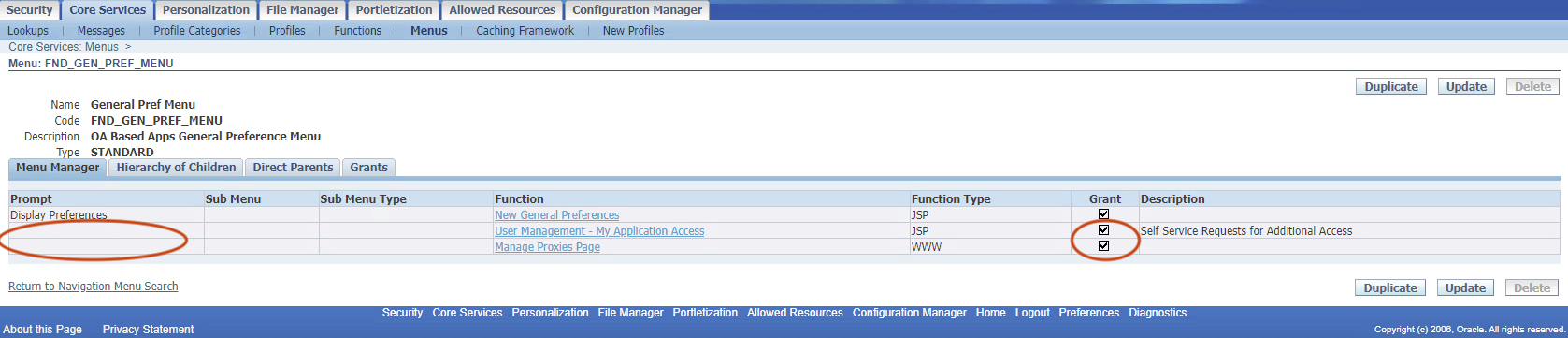
1. Login as SYSADMIN and navigate to Functional Administrator > Home > Core Services > Menus
2. Search for Code = FND_GEN_PREF_MENU
3. Remove the prompt for "User Management - My Application Access" and "Manage Proxies Page".
4. Uncheck the Grant checkbox for both.
R12.2
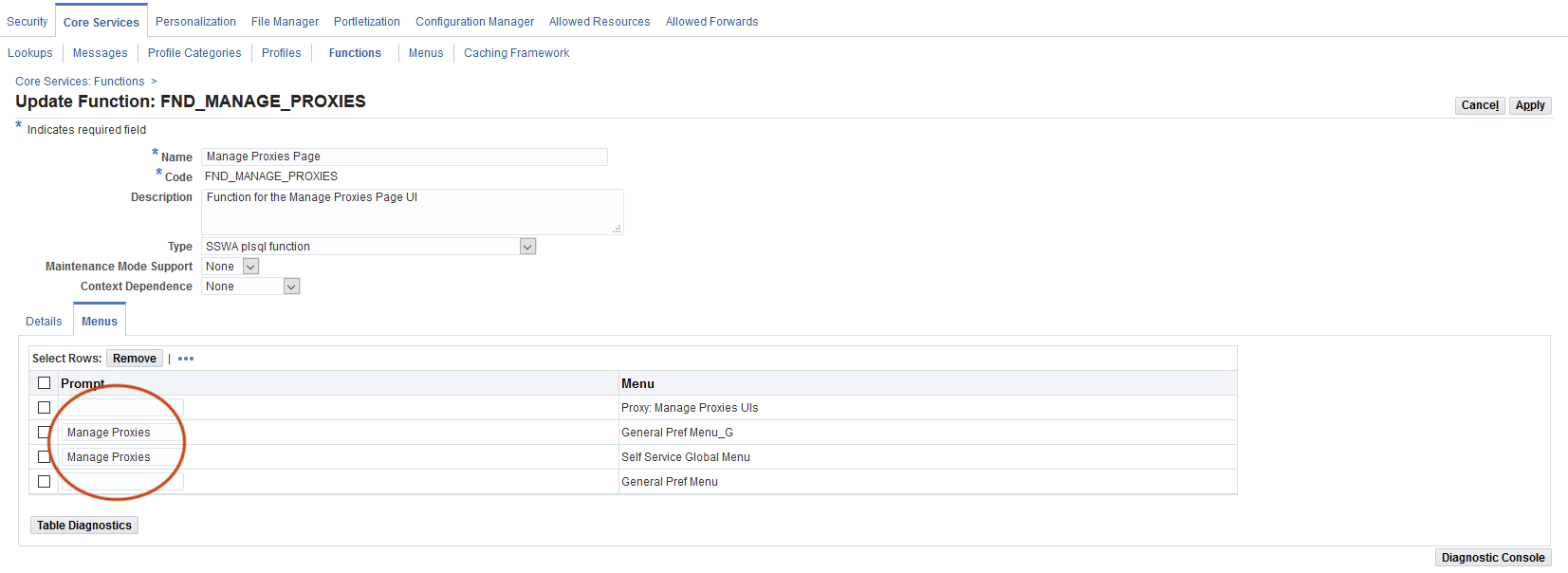
I. To remove the Manage Proxies function:
1. Login as SYSADMIN and navigate to Functional Administrator > Home > Core Services > Functions
2. Search for Name = Manage Proxies
3. Manage Proxies Page > Update
4. Click on Menus tab
5. Then remove the prompt.
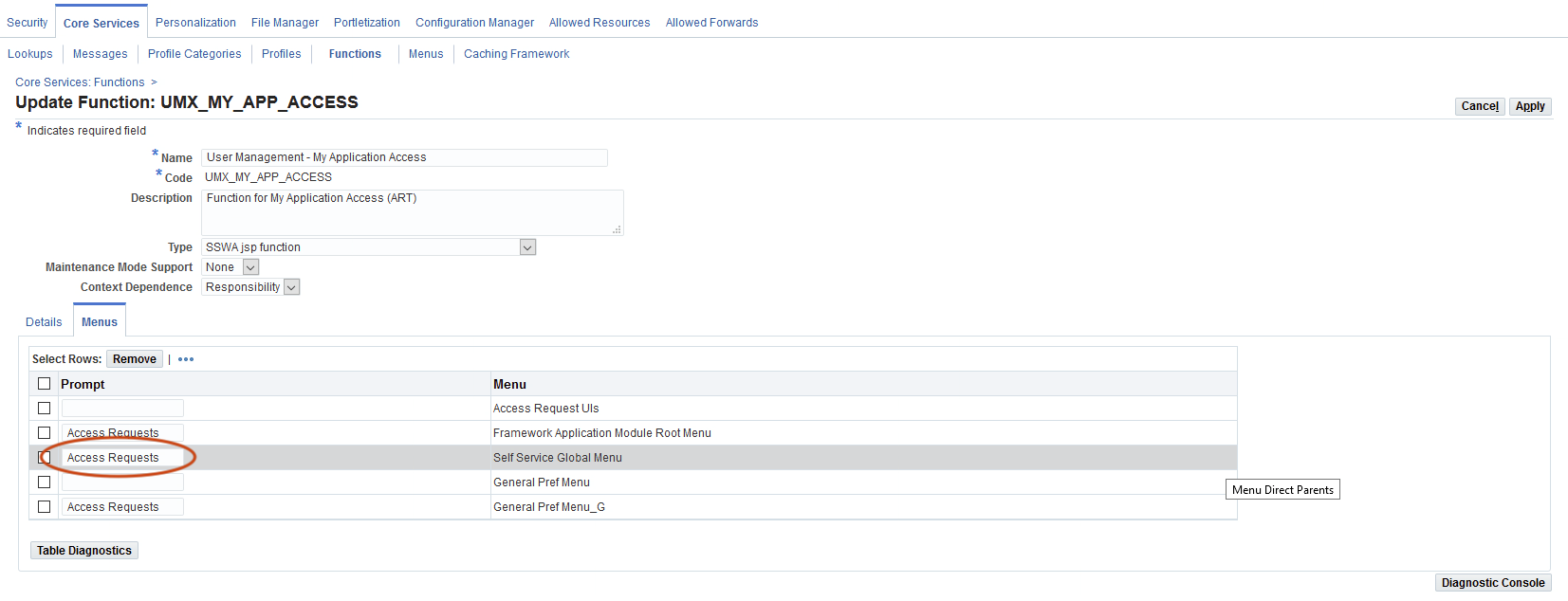
II. To remove the Access Request Menu Item from Homepage:
1. Query "User Management - My Application Access" under the Functions tab.
2. Click Update
3. Remove from "Self Service Global Menu"
4. Clear the functional cache (Core Services > Caching Framework > Global Configuration > Clear All Cache)
5. All Users in Proxy Delegation Privilege
The official note states that we need to update the Proxy Delegation Privilege and select the Selected Roles or Responsibilities option instead of All Users.
1. Login as SYSADMIN and navigate to User Management > Home > Proxy Configuration > Privileges
2. Switch to the Selected Roles or Responsibilities option:
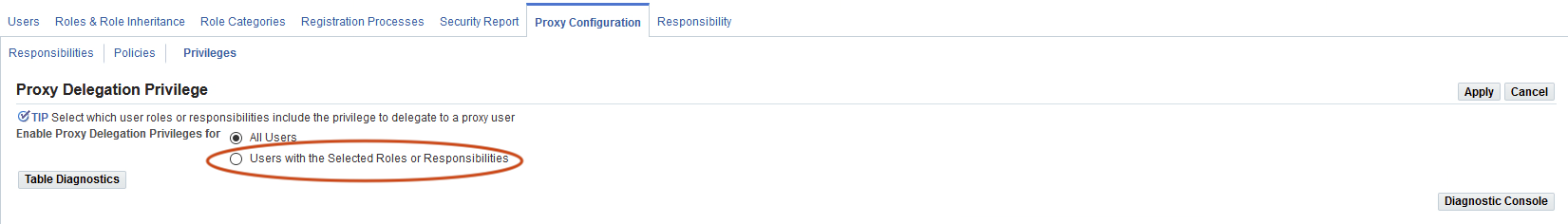
IMPORTANT: This is an R12.2 feature and does not exist in R12.1 unless you have applied Patch 19804456 BACKPORT REQUEST FOR UMX GRANULAR PROXY MANAGER FOR 12.1.X. If you have not, you have the default All Users behavior.
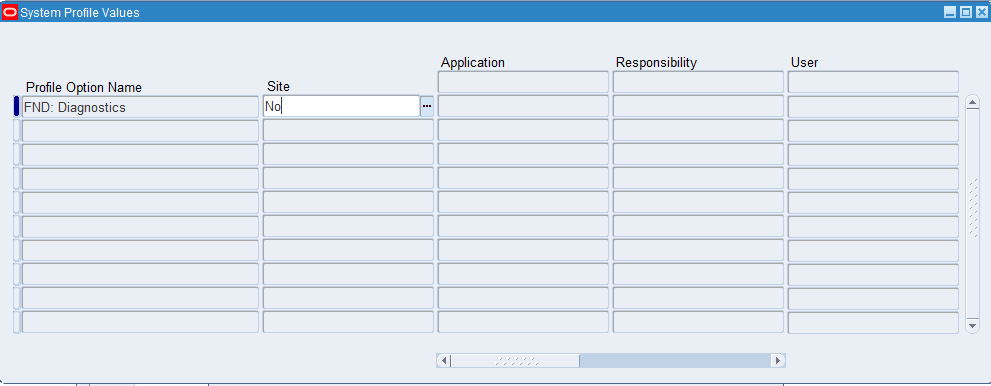
6. Turn off “FND: Diagnostics” on the Site level
It is a general security recommendation always to have the FND diagnostics disabled on the Site level. Enable it only for users and responsibilities as required:
References
- https://orwaatyat.medium.com/my-new-discovery-in-oracle-e-business-login-panel-that-allowed-to-access-for-all-employees-ed0ec4cad7ac
- https://www.oracle.com/security-alerts/alert-cve-2022-21500.html
- Security Alert CVE-2022-21500 Patch Availability Document for Oracle E-Business Suite (Doc ID 2870472.1)
- How To Personalize Login Page To Show Or Hide Links on EBS 12.2.5+ (Doc ID 2105595.1)
- E-Business Suite R12 : Steps To Remove Functions ‘Access Requests’ And ‘Manage Proxies’ From The ‘Preferences’ Page (Doc ID 2182942.1)
We will update this post as updates develop. Feel free to reach out to us if you need any help with the security review of your EBS system.

